Let’s say you have a 256 bit encryption key in some piece of hardware. How do you keep it secure? Turns out, it’s very, very hard. Especially when the actual device can be in the hands of those that want to crack it.
I used to work in a company that made failure analysis equipment for chips. It used a high gain intensified video camera to look for light emissions from bad transistors. What was neat about it is that you could see the light from the active layer through all the interconnects and the like. And when the number of metal layers got too high for that, you could see the light that made it through the silicon itself by looking at the other side of the die. While this is a bit off topic, while I did work there I did run into someone who worked for the NSA or some other government acronym that asked me how can you keep the function of a device secret from someone who has it in their hands. And this got me thinking (oh no, here we go again….)
Off the top of my head I had few answers for him. Dummy circuits can confuse the issue. The only real good idea I had was to make the device somewhat self-destructive if probed. Turns out that is what some companies are starting to do.
First, a bit about how you can figure out what’s inside the digital vault, so to speak. (I learned a lot about this from Paul Kocher, creator of SSL encryption that’s on all of our computers. His company is Cryptography Research Inc.) First off, you can use brute force and just querie the target over and over till you get it right. With enough bits, this takes a lot of CPU power and time, and gets very expensive.

In fact, while high bit count security features add complexity that increases the time and cost required to figure it out, there are shortcuts available….

What I found interesting here is that brute force is often not the easiest way to crack the algorithm. Flaws in system design and human nature often provide much easier ways in that just guessing keys. But look at that little box at the top of the graphic that says “Buy FIB” That stands for Focused Ion Beam machine and it can take apart a chip atom by atom to really find out what’s going on in the guts of an encryption IC. It’s not cheap, and it’s not that fast, but it works. So if you can get your hand on the actual encryption engine silicon, all the secrets can be found out. It’s not an “if” it’s a “when”. This matters a lot if you want to do something like have secure communication with a cruise missile or something like that.
But it turns out that you don’t have to go quite this far for some situations. There’s something called the “transistor effect”… and that means if you look at the power lines of a chip, you can see what it’s doing! (Big effin surprise for a lot of people!)

Damn! All that money into key development and now you tell me that you can read it like a teletype tape! So what to do? Well, you can minimize this effect but the net result is that the technique still works, it just takes more time and money to implement. So this leads to a couple of things.
The first is the never ending see-saw of increased security and changing threat. This is a back and forth battle that never ends. You see it every day in the updates to your operating system and new threat files for your anti-virus and mal-ware filters. Plug one hole and the enemy find another…. Back and forth pretty much forever.
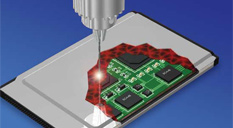
But there’s another trick that W. L. Gore is offering (not for your laptop, but for hardware that requires security). It’s a polymer circuit that goes around the device in question, and when it detect a breach, the device can be wiped or destroyed (depending on your level of paranoia).
Now back to my good idea. This wrapper detects penetration attempts and then the circuit can take care of itself. While this is just another round in the data security war, it seems like a pretty good one to me.
Share This: